Best Remote IoT SSH Key Management: A Comprehensive Guide For Secure Connections
Mar 22 2025
In today's interconnected world, the best remote IoT SSH key management practices are essential for maintaining secure communications between devices. With the rapid growth of Internet of Things (IoT) technology, organizations are increasingly adopting remote device management solutions. However, ensuring secure access through SSH keys is a critical component that cannot be overlooked. In this article, we will explore the most effective strategies for managing SSH keys in remote IoT environments, helping you protect your network and data.
SSH keys have become an indispensable tool for secure communication in the digital age. They provide a reliable method of authentication for remote access, eliminating the need for passwords and reducing the risk of unauthorized access. However, as the number of IoT devices grows, managing SSH keys efficiently becomes a complex challenge. This article delves into the best practices, tools, and strategies for managing SSH keys in remote IoT environments.
Whether you're a system administrator, IT professional, or cybersecurity expert, understanding the nuances of SSH key management is vital for ensuring the security of your IoT infrastructure. In this comprehensive guide, we will cover everything you need to know about securing your IoT devices through effective SSH key management. Let's dive in!
Table of Contents
- What is Remote IoT SSH Key Management?
- Why Is SSH Key Management Important for IoT?
- Best Practices for Remote IoT SSH Key Management
- Top Tools for Managing SSH Keys in IoT
- Securing SSH Keys in IoT Networks
- Common Risks in IoT SSH Key Management
- Scaling SSH Key Management for Large IoT Deployments
- Automation in SSH Key Management
- Compliance and Regulatory Considerations
- The Future of IoT SSH Key Management
What is Remote IoT SSH Key Management?
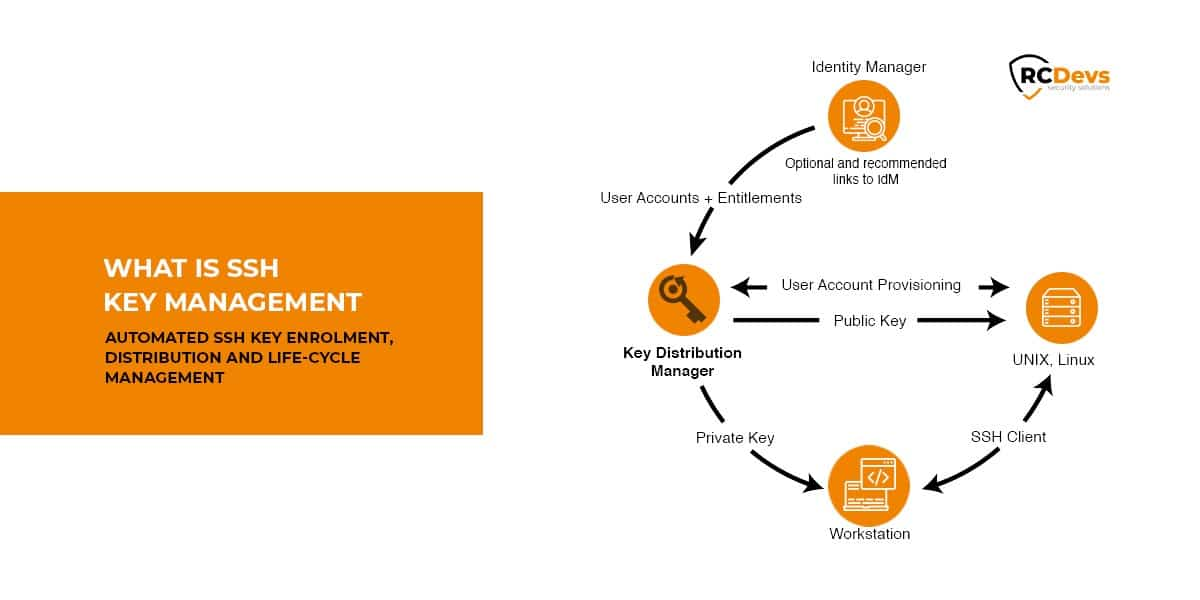
Remote IoT SSH key management refers to the process of securely handling SSH keys used for authenticating and authorizing access to IoT devices located remotely. SSH (Secure Shell) keys are cryptographic keys that replace traditional password-based authentication, providing a more secure and efficient method for accessing devices over a network.
In the context of IoT, managing SSH keys becomes even more complex due to the sheer number of devices involved. Each device requires its own unique SSH key pair, and keeping track of these keys can be a daunting task without proper tools and strategies. Effective SSH key management ensures that only authorized users and devices can access the network, reducing the risk of cyberattacks and data breaches.
Key Components of Remote IoT SSH Key Management
The process of managing SSH keys in IoT environments involves several key components:
- Key generation: Creating strong and unique SSH key pairs for each device.
- Key distribution: Safely distributing public keys to authorized devices and users.
- Key rotation: Regularly updating and replacing old SSH keys to maintain security.
- Key revocation: Removing or disabling SSH keys that are no longer needed or have been compromised.
Why Is SSH Key Management Important for IoT?
SSH key management plays a crucial role in securing IoT networks. As IoT devices become more prevalent, the potential attack surface for cybercriminals grows exponentially. Without proper SSH key management, organizations risk exposing sensitive data and allowing unauthorized access to critical systems.
Here are some reasons why SSH key management is so important in IoT:
- Enhanced security: SSH keys provide a stronger form of authentication compared to passwords, reducing the risk of brute-force attacks and credential theft.
- Scalability: Managing SSH keys allows organizations to efficiently scale their IoT deployments without compromising security.
- Compliance: Many industries have strict regulations regarding data security and access control, making SSH key management a necessity for compliance.
Best Practices for Remote IoT SSH Key Management
To ensure the security and efficiency of your IoT infrastructure, it's essential to follow best practices for SSH key management. Here are some key strategies to consider:
1. Use Strong SSH Keys
Always use strong, high-bit-length SSH keys (e.g., 2048-bit RSA or 256-bit ECDSA) to ensure maximum security. Avoid using outdated or weak algorithms that can be easily compromised.
2. Limit Key Lifespan
Set expiration dates for SSH keys to ensure they are regularly updated. This reduces the risk of keys being compromised over time and ensures that only current keys are active in your system.
3. Implement Key Rotation
Regularly rotate SSH keys to minimize the impact of any potential key compromise. Automating this process can help reduce administrative overhead and ensure consistency.
Top Tools for Managing SSH Keys in IoT
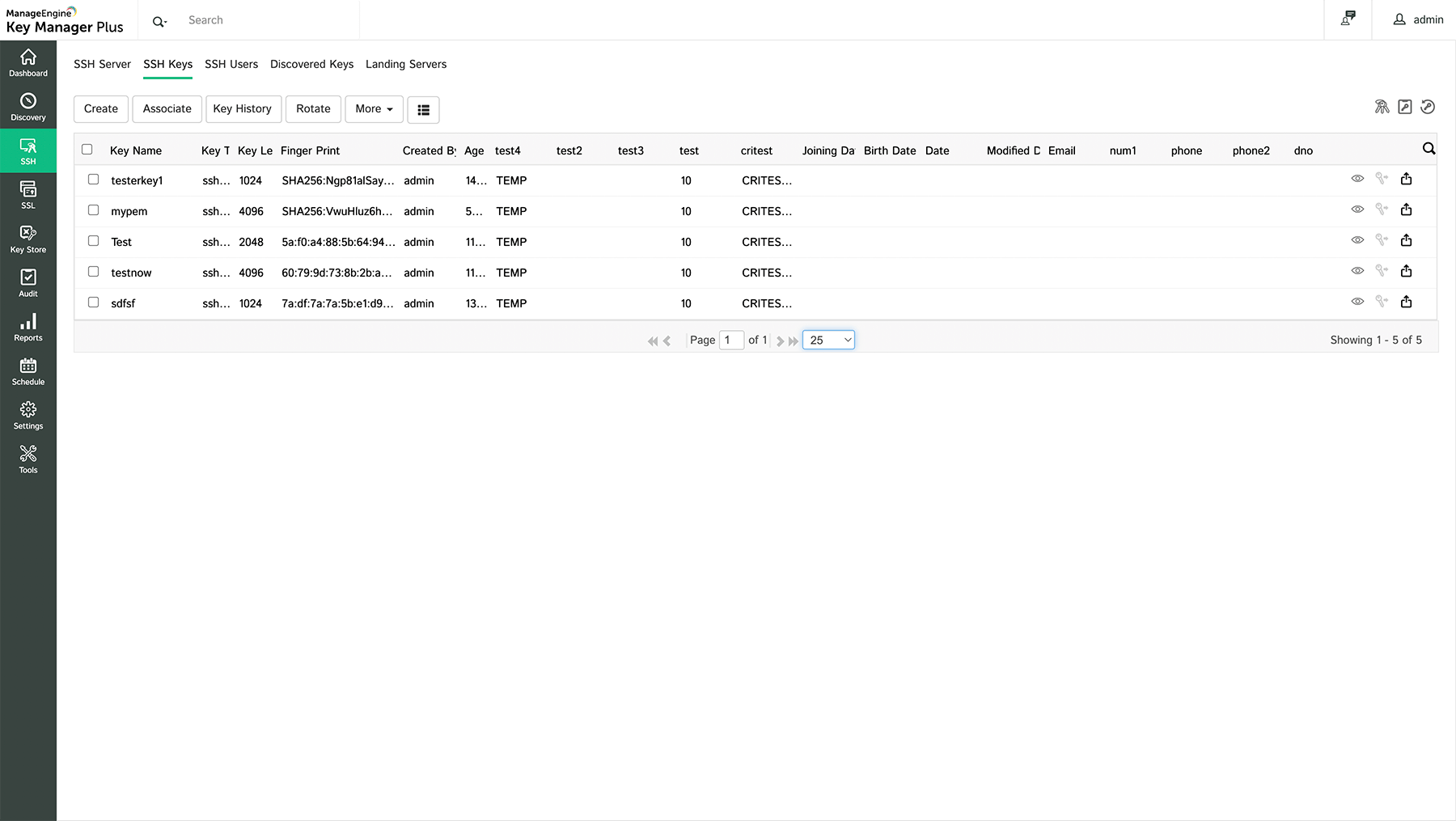
Several tools and platforms are available to assist with SSH key management in IoT environments. These tools offer features such as automated key generation, distribution, and rotation, making it easier to maintain secure and efficient SSH key management practices.
1. HashiCorp Vault
HashiCorp Vault is a popular tool for managing secrets, including SSH keys. It provides secure storage, automated key rotation, and fine-grained access control, making it an ideal choice for IoT deployments.
2. SSH Key Manager
SSH Key Manager is a dedicated solution for managing SSH keys across large-scale environments. It offers features such as key discovery, revocation, and reporting, ensuring comprehensive control over your SSH key infrastructure.
Securing SSH Keys in IoT Networks
Securing SSH keys in IoT networks requires a multi-layered approach that combines technical measures with organizational policies. Here are some strategies to enhance the security of your SSH key management process:
1. Use Hardware Security Modules (HSMs)
HSMs provide a secure environment for storing and managing cryptographic keys, reducing the risk of unauthorized access. Integrating HSMs into your SSH key management process can significantly enhance security.
2. Enable Two-Factor Authentication (2FA)
Implementing 2FA for SSH access adds an extra layer of security, ensuring that even if a key is compromised, unauthorized access remains difficult to achieve.
Common Risks in IoT SSH Key Management
Despite the benefits of SSH key management, there are several risks associated with improper implementation. These risks can lead to security vulnerabilities and data breaches if not addressed properly.
1. Untracked SSH Keys
When SSH keys are not properly tracked and managed, they can become "orphaned," meaning they remain active even after the associated user or device is no longer needed. This creates a significant security risk, as these keys can be exploited by attackers.
2. Weak or Default Keys
Using weak or default SSH keys can make your IoT devices vulnerable to attacks. Always ensure that keys are strong, unique, and generated using secure algorithms.
Scaling SSH Key Management for Large IoT Deployments
As IoT deployments grow in size and complexity, scaling SSH key management becomes a critical challenge. Organizations must implement scalable solutions that can handle thousands or even millions of devices without compromising performance or security.
1. Centralized Management
Using a centralized management platform allows organizations to efficiently manage SSH keys across large-scale IoT deployments. This approach simplifies key tracking, distribution, and revocation, ensuring consistency and security.
2. Automation
Automating key generation, distribution, and rotation can significantly reduce the administrative burden associated with managing SSH keys in large IoT environments. Automation also helps ensure that best practices are consistently applied across all devices.
Automation in SSH Key Management
Automation plays a vital role in modern SSH key management practices. By automating repetitive tasks such as key generation, distribution, and rotation, organizations can reduce errors, improve efficiency, and enhance security.
1. Scripting and APIs
Using scripting languages and APIs, organizations can automate various aspects of SSH key management. This approach allows for greater flexibility and customization, enabling organizations to tailor their processes to their specific needs.
2. Integration with Existing Systems
Integrating SSH key management tools with existing IT infrastructure ensures seamless operation and reduces the need for manual intervention. This can lead to improved security and better overall management of IoT devices.
Compliance and Regulatory Considerations
Many industries have strict regulations regarding data security and access control, making compliance a key consideration in SSH key management. Organizations must ensure that their SSH key management practices meet relevant standards and regulations to avoid penalties and maintain trust with customers.
1. GDPR
The General Data Protection Regulation (GDPR) requires organizations to implement robust security measures to protect personal data. Proper SSH key management is essential for ensuring compliance with GDPR requirements.
2. HIPAA
The Health Insurance Portability and Accountability Act (HIPAA) mandates strict controls over access to sensitive health information. Organizations handling medical data must ensure that their SSH key management processes meet HIPAA standards.
The Future of IoT SSH Key Management
As IoT technology continues to evolve, so too will the methods and tools used for SSH key management. Emerging technologies such as blockchain and quantum cryptography may play a significant role in shaping the future of secure communication in IoT environments.
Organizations must stay informed about the latest developments in SSH key management to ensure they remain at the forefront of cybersecurity best practices. By adopting innovative solutions and staying ahead of potential threats, organizations can protect their IoT infrastructure and maintain the trust of their customers.
Conclusion
In conclusion, effective SSH key management is essential for securing remote IoT devices and maintaining the integrity of your network. By following best practices, utilizing the right tools, and staying informed about emerging trends, you can ensure that your SSH key management processes remain robust and secure.
We encourage you to take action by implementing the strategies outlined in this article. Leave a comment below to share your thoughts or ask questions, and don't forget to explore other articles on our site for more valuable insights into IoT security and beyond. Together, we can build a safer and more connected world.