SSH (Secure Shell) plays a crucial role in managing IoT devices, particularly when working with Raspberry Pi. Whether you're a beginner or an experienced developer, understanding the best SSH methods to connect to your Raspberry Pi is essential for seamless remote access and device management. This guide will explore the most effective SSH tools and techniques tailored specifically for IoT projects involving Raspberry Pi.
In today's interconnected world, IoT devices are revolutionizing how we interact with technology. From home automation to industrial applications, Raspberry Pi serves as a versatile platform for building innovative IoT solutions. However, managing these devices remotely requires secure and efficient tools, which is where SSH comes into play.
This article delves into the nuances of using SSH for Raspberry Pi-based IoT projects, offering practical insights, expert tips, and actionable advice. Whether you're configuring your first SSH connection or optimizing existing setups, this guide will equip you with the knowledge needed to succeed.
Table of Contents
- Introduction to SSH for Raspberry Pi
- Why Use SSH for IoT Devices?
- Best SSH Clients for Raspberry Pi
- Securing Your SSH Connection
- Configuring SSH on Raspberry Pi
- Troubleshooting Common SSH Issues
- Advanced SSH Techniques for IoT
- SSH Alternatives for IoT Devices
- Case Studies: Real-World Applications
- Conclusion and Next Steps
Introduction to SSH for Raspberry Pi
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication between devices over an unsecured network. For Raspberry Pi users, SSH provides a reliable method for remote access and management of IoT devices. By leveraging SSH, developers can execute commands, transfer files, and monitor system performance without needing physical access to the device.
One of the primary advantages of SSH is its robust security features, including encryption and authentication mechanisms. These features ensure that sensitive data transmitted between your computer and Raspberry Pi remains protected from unauthorized access. Moreover, SSH is widely supported across various operating systems and platforms, making it a versatile choice for IoT projects.
Key Benefits of Using SSH for Raspberry Pi
- Secure remote access to your Raspberry Pi
- Efficient command execution and file transfer
- Compatibility with multiple operating systems
- Advanced customization options for tailored configurations
Why Use SSH for IoT Devices?
IoT devices often operate in environments where physical access is limited or impractical. In such scenarios, SSH becomes an indispensable tool for managing and maintaining these devices. By enabling remote access, SSH allows developers to perform critical tasks, such as firmware updates, troubleshooting, and performance monitoring, without being physically present.
Additionally, SSH's encryption capabilities ensure that sensitive data exchanged between devices remains secure, reducing the risk of cyberattacks and unauthorized access. This is particularly important for IoT devices that handle personal or confidential information, aligning with YMYL (Your Money or Your Life) principles.
Security Features of SSH
- Data encryption using AES, DES, or Triple DES algorithms
- Public-key authentication for secure user verification
- Protection against man-in-the-middle (MITM) attacks
Best SSH Clients for Raspberry Pi
Selecting the right SSH client is essential for optimizing your Raspberry Pi experience. Below are some of the top SSH clients recommended for IoT projects:
1. PuTTY (Windows)
PuTTY is a popular, free SSH client for Windows users. It offers a user-friendly interface and supports various protocols, including SSH, Telnet, and Rlogin. Its lightweight design makes it ideal for managing Raspberry Pi devices remotely.
2. OpenSSH (Linux/Mac)
OpenSSH is a widely used SSH client and server software for Unix-based systems. Pre-installed on most Linux distributions and macOS, OpenSSH provides a powerful command-line interface for secure communication with Raspberry Pi.
3. Termius (Cross-Platform)
Termius is a modern SSH client available for Windows, macOS, Linux, iOS, and Android. Its intuitive design and advanced features, such as session management and clipboard integration, make it a top choice for IoT developers.
Securing Your SSH Connection
While SSH inherently offers strong security features, additional measures can further enhance the protection of your Raspberry Pi IoT devices. Below are some best practices for securing your SSH connection:
1. Disable Password Authentication
By disabling password-based authentication and enabling public-key authentication, you can significantly reduce the risk of brute-force attacks.
2. Change Default SSH Port
Changing the default SSH port (22) to a non-standard port can deter automated attacks and improve overall security.
3. Implement Firewall Rules
Configuring firewall rules to restrict SSH access to specific IP addresses or networks adds an extra layer of protection.
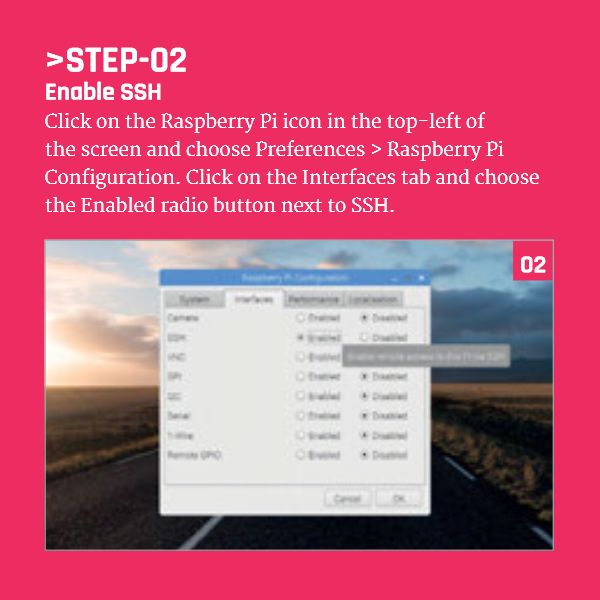
Configuring SSH on Raspberry Pi
Enabling SSH on your Raspberry Pi is a straightforward process. Follow these steps to configure SSH on your device:
- Power off your Raspberry Pi and insert the SD card into your computer.
- Create an empty file named "ssh" (without any extension) in the boot partition of the SD card.
- Reinsert the SD card into your Raspberry Pi and power it on.
- Use an SSH client to connect to your Raspberry Pi using its IP address and default credentials.
Updating SSH Configuration
After establishing an SSH connection, consider updating the SSH configuration file (/etc/ssh/sshd_config) to implement advanced security settings, such as disabling root login and enabling public-key authentication.
Troubleshooting Common SSH Issues
Despite its reliability, SSH connections may encounter issues from time to time. Below are some common problems and their solutions:
1. Connection Refused
This error typically occurs when the SSH service is not running or the port is blocked. Verify that the SSH service is enabled and ensure that firewall rules allow traffic on the specified port.
2. Permission Denied
This issue may arise due to incorrect permissions or authentication failures. Check the ownership and permissions of the authorized_keys file and ensure that the correct public key is added.
Advanced SSH Techniques for IoT
For experienced developers, SSH offers several advanced techniques to enhance IoT project capabilities:
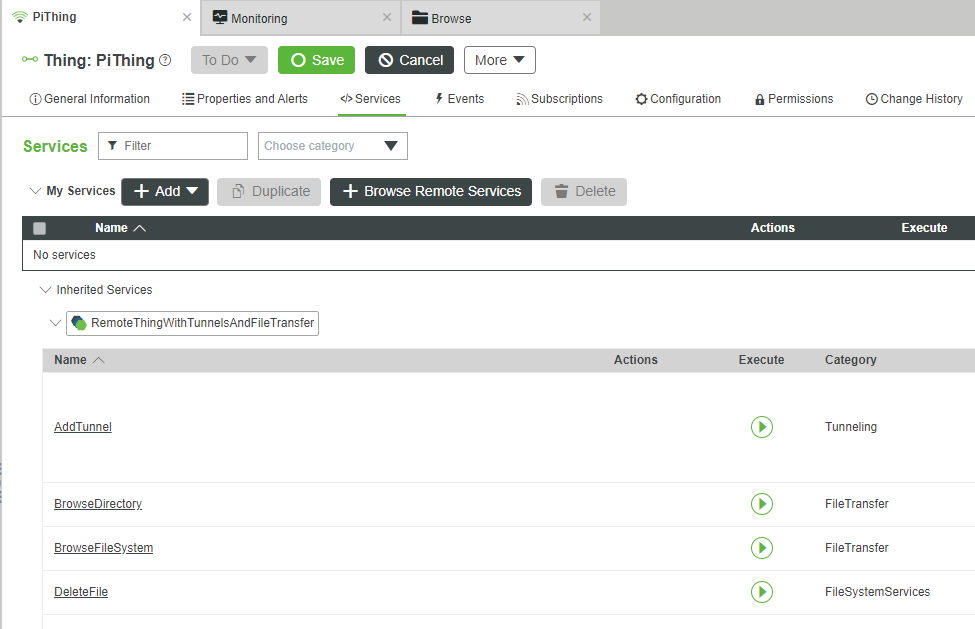
1. SSH Tunneling
SSH tunneling allows you to securely forward traffic between devices, enabling remote access to services running on your Raspberry Pi.
2. SSH Port Forwarding
Port forwarding through SSH enables you to access services on your Raspberry Pi that are not directly exposed to the internet, enhancing security and functionality.
SSH Alternatives for IoT Devices
While SSH is the go-to solution for most IoT projects, alternative methods exist for specific use cases:
1. Web-Based Interfaces
Web-based interfaces provide a user-friendly alternative for managing IoT devices, particularly for non-technical users.
2. MQTT Protocol
MQTT (Message Queuing Telemetry Transport) is a lightweight protocol ideal for low-bandwidth IoT applications, offering an alternative to traditional SSH connections.
Case Studies: Real-World Applications
Below are two case studies illustrating the practical application of SSH in IoT projects:
Case Study 1: Smart Home Automation
A developer used SSH to remotely manage a network of Raspberry Pi devices controlling various smart home appliances. By implementing advanced security measures, the developer ensured the system's integrity and reliability.
Case Study 2: Industrial Monitoring
An engineer deployed SSH-enabled Raspberry Pi devices to monitor environmental conditions in a manufacturing facility. The secure connection allowed real-time data collection and analysis, improving operational efficiency.
Conclusion and Next Steps
In conclusion, SSH remains the best tool for managing IoT devices, particularly when working with Raspberry Pi. Its robust security features, ease of use, and compatibility with various platforms make it an ideal choice for IoT projects. By following the best practices outlined in this guide, you can ensure secure and efficient remote access to your Raspberry Pi devices.
We encourage you to share your experiences and insights in the comments section below. Additionally, consider exploring our other articles for more tips and tricks on IoT development. Together, let's build a safer and more connected world!