RemoteIoT platform SSH key has become an essential component for ensuring secure access to IoT devices. As the Internet of Things (IoT) continues to grow, securing devices remotely is crucial for preventing unauthorized access and potential cyber threats. In this article, we will explore everything you need to know about RemoteIoT platform SSH key and how it can enhance your security measures.
The rise of connected devices in homes, businesses, and industries has made it imperative to adopt robust security protocols. RemoteIoT platform SSH key offers a secure way to authenticate users and manage access to IoT devices. This technology ensures that only authorized personnel can interact with these devices, safeguarding sensitive data and operations.
In this comprehensive guide, we will delve into the intricacies of RemoteIoT platform SSH key, its benefits, implementation, and best practices. Whether you're a developer, IT professional, or simply interested in IoT security, this article will provide valuable insights to help you secure your IoT ecosystem.
Table of Contents
- Introduction to RemoteIoT Platform SSH Key
- What is SSH?
- Benefits of Using SSH Keys
- Overview of RemoteIoT Platform
- Implementing SSH Keys on RemoteIoT
- Best Practices for SSH Key Management
- Security Considerations
- Troubleshooting Common Issues
- Use Cases for RemoteIoT Platform SSH Key
- Future Trends in IoT Security
Introduction to RemoteIoT Platform SSH Key
RemoteIoT platform SSH key plays a pivotal role in securing IoT devices by enabling secure communication and access control. SSH (Secure Shell) is a cryptographic network protocol that facilitates secure data communication, remote command execution, and file transfer. By integrating SSH keys into the RemoteIoT platform, organizations can enhance their security posture and protect against unauthorized access.
SSH keys offer a more secure alternative to traditional password-based authentication. They provide a two-factor authentication mechanism, where users must possess both the private key and the passphrase to gain access. This significantly reduces the risk of brute-force attacks and password guessing.
As IoT devices become increasingly interconnected, the need for robust security measures has never been greater. RemoteIoT platform SSH key addresses this need by offering a scalable and secure solution for managing access to IoT devices.
What is SSH?
Understanding SSH Protocol
SSH, or Secure Shell, is a network protocol that provides secure communication over unsecured networks. It encrypts all data transmitted between a client and server, ensuring that sensitive information remains confidential. SSH is widely used for remote system administration, file transfers, and tunneling.
Key features of SSH include:
- Encryption of data in transit
- Authentication using public-key cryptography
- Support for various encryption algorithms
How SSH Works
SSH operates by establishing a secure connection between a client and a server. The process involves:
- Key exchange to establish a shared secret
- Authentication using public and private keys
- Encryption of all subsequent communication
This ensures that even if the communication is intercepted, the data remains unreadable to unauthorized parties.
Benefits of Using SSH Keys
Using SSH keys offers several advantages over traditional password-based authentication. Some of the key benefits include:
- Enhanced Security: SSH keys provide stronger authentication than passwords, reducing the risk of unauthorized access.
- Convenience: Once set up, SSH keys allow for seamless access without the need to repeatedly enter passwords.
- Scalability: SSH keys can be easily managed across multiple devices and users, making them ideal for large-scale deployments.
- Automation: SSH keys enable automated processes, such as script execution and file transfers, without requiring user intervention.
These benefits make SSH keys an essential tool for securing IoT devices and ensuring reliable access.
Overview of RemoteIoT Platform
What is RemoteIoT Platform?
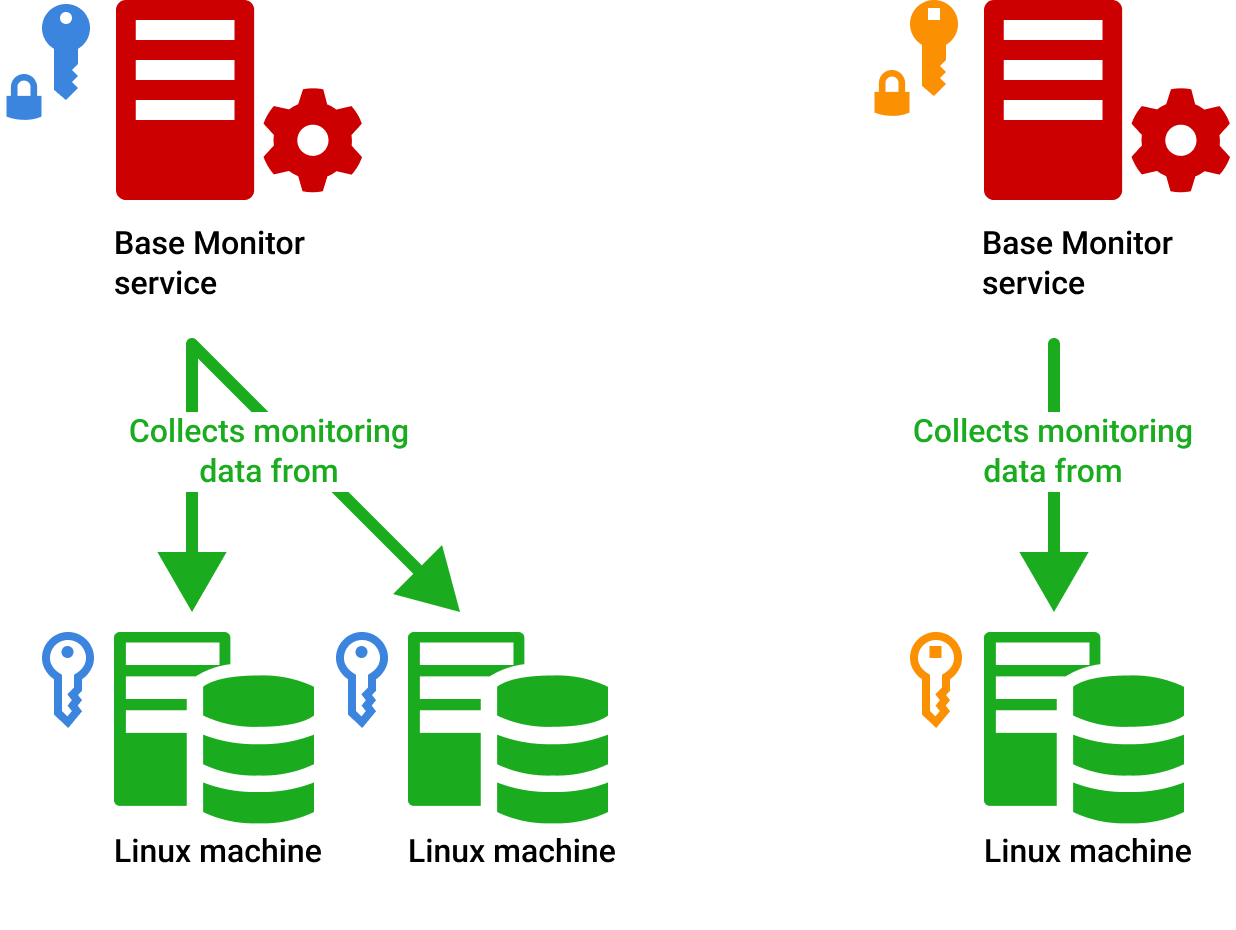
RemoteIoT platform is a comprehensive solution for managing IoT devices remotely. It provides tools for device monitoring, configuration, and troubleshooting, all while ensuring secure access through SSH keys. The platform supports a wide range of IoT devices, making it suitable for various industries, including manufacturing, healthcare, and smart cities.
Key Features of RemoteIoT Platform
Some of the key features of RemoteIoT platform include:
- Centralized device management
- Secure access control using SSH keys
- Real-time monitoring and alerts
- Customizable dashboards
These features enable organizations to efficiently manage their IoT infrastructure while maintaining a high level of security.
Implementing SSH Keys on RemoteIoT
Step-by-Step Guide
Implementing SSH keys on RemoteIoT platform involves the following steps:
- Generate SSH key pairs on your local machine
- Upload the public key to the RemoteIoT platform
- Configure device settings to accept SSH connections
- Test the connection to ensure secure access
By following these steps, you can ensure that your IoT devices are securely accessible through the RemoteIoT platform.
Best Practices for Implementation
When implementing SSH keys on RemoteIoT platform, consider the following best practices:
- Use strong, unique passphrases for private keys
- Regularly rotate SSH keys to minimize the risk of compromise
- Limit access to private keys to authorized personnel only
These practices will help you maintain the integrity and security of your SSH keys.
Best Practices for SSH Key Management
Effective SSH key management is crucial for maintaining the security of your IoT ecosystem. Here are some best practices to follow:
- Inventory all SSH keys and their associated users
- Set expiration dates for SSH keys to enforce regular rotation
- Monitor and audit SSH key usage regularly
- Use key management tools to streamline the process
By adhering to these best practices, you can ensure that your SSH keys remain secure and effective.
Security Considerations
Potential Vulnerabilities
While SSH keys offer strong security, they are not immune to vulnerabilities. Some potential risks include:
- Private key exposure due to weak passphrases
- Insufficient key rotation policies
- Unsecured storage of private keys
It is essential to address these vulnerabilities to maintain the security of your SSH keys.
Protecting Against Attacks
To protect against attacks, consider implementing the following measures:
- Enable two-factor authentication for additional security
- Use intrusion detection systems to monitor for suspicious activity
- Regularly update SSH software to patch known vulnerabilities
These measures will help you mitigate potential threats and ensure the integrity of your SSH keys.
Troubleshooting Common Issues
Common Problems
Some common issues users may encounter when using SSH keys on RemoteIoT platform include:
- Connection refused due to incorrect key configuration
- Timeouts caused by network latency
- Authentication failures due to expired keys
By identifying these issues early, you can address them promptly and avoid disruptions to your IoT operations.
Solutions and Tips
To resolve these issues, consider the following solutions:
- Double-check key configurations for accuracy
- Optimize network settings to reduce latency
- Regularly update and rotate SSH keys
These tips will help you maintain a stable and secure connection to your IoT devices.
Use Cases for RemoteIoT Platform SSH Key
Industry Applications
RemoteIoT platform SSH key finds applications in various industries, including:
- Manufacturing: Securely monitor and control industrial IoT devices
- Healthcare: Protect sensitive patient data and medical equipment
- Smart Cities: Manage smart infrastructure and public services
These use cases demonstrate the versatility and importance of SSH keys in securing IoT ecosystems.
Real-World Examples
Several organizations have successfully implemented RemoteIoT platform SSH key to enhance their security. For example, a manufacturing company used SSH keys to secure access to their production line IoT devices, reducing downtime and improving operational efficiency.
Future Trends in IoT Security
As IoT continues to evolve, so too will the methods for securing these devices. Some future trends in IoT security include:
- Increased adoption of quantum-resistant encryption
- Integration of AI and machine learning for threat detection
- Development of standardized security protocols
By staying informed about these trends, organizations can prepare for the future of IoT security and ensure their systems remain protected.
Conclusion
RemoteIoT platform SSH key offers a comprehensive solution for securing IoT devices and ensuring reliable access. By understanding the benefits, implementation steps, and best practices, you can effectively integrate SSH keys into your IoT ecosystem and enhance your security measures.
We encourage you to take action by implementing SSH keys on your RemoteIoT platform and sharing your experiences with the community. For more information on IoT security, explore our other articles and resources.
References:
- OpenSSH Documentation - https://www.openssh.com/
- NIST Cybersecurity Framework - https://www.nist.gov/cyberframework